Crack STM32F101R8 MCU Flash Memory
Crack STM32F101R8 MCU Flash Memory: Methods and Techniques
The STM32F101R8 MCU is designed with robust security features to prevent unauthorized access to its flash memory and firmware. However, in cases where legitimate recovery is needed, various techniques can be employed to unlock the protected data and extract the binary or source code from the microcontroller. These methods involve reverse engineering, decapsulating the chip, and using advanced attack strategies to bypass security mechanisms.
Understanding the Security of STM32F101R8
The secured STM32F101R8 MCU features flash read protection to prevent unauthorized access to stored firmware and heximal files. This protection makes direct reading or copying of the memory difficult. To break this protection, researchers and engineers often utilize hardware-based or software-based techniques to decrypt the locked content.
Methods to Crack and Dump Flash Memory
1. Voltage Glitching and Fault Injection Attack
One way to hack the microcontroller is by inducing voltage glitches during boot-up, which can disable the security settings momentarily, allowing access to the flash memory. A similar attack method is fault injection, where precise pulses are sent to the chip to cause unexpected behavior and bypass security restrictions.

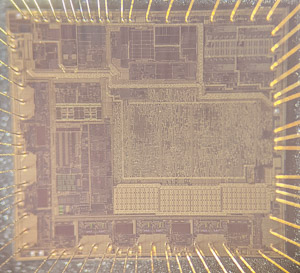
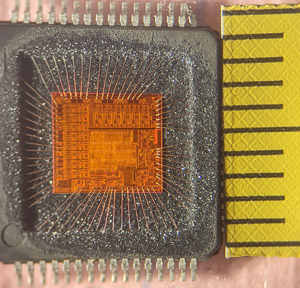
2. Decapsulation and Microprobing
For advanced reverse engineering, decapsulation techniques can be applied to physically open the MCU package and expose the microprocessor die. Using microprobing tools, it is possible to read the protected flash memory directly, allowing for binary extraction and firmware dumping.
3. Side-Channel Analysis (SCA)
By analyzing the power consumption patterns or electromagnetic emissions of the MCU during operation, one can infer critical security details. This method can help to decrypt or decode the encrypted data stored in the flash memory.
4. Software Exploitation and Debugging
Some locked STM32 microcontrollers may have firmware vulnerabilities that allow access through debug ports. In certain cases, using JTAG/SWD interfaces with modified bootloader code can help open the flash memory for extraction.
Conclusion
While various techniques exist to crack the STM32F101R8 MCU flash memory, it is essential to ensure that these methods are applied within legal and ethical boundaries. Unauthorized attempts to replicate, duplicate, or extract protected data can lead to legal consequences. Always seek proper authorization before performing any attack on a secured system.
These timers are based on a 16-bit auto-reload upcounter and a 16-bit prescaler. TIM15 has two independent channels, whereas TIM16 and TIM17 feature one single channel for input capture/output compare, PWM or one-pulse mode output by Crack STM32F101R8 MCU Flash Memory. The TIM15, TIM16 and TIM17 timers can work together, and TIM15 can also operate with TIM1 via the Timer Link feature for synchronization or event chaining through Reverse Engineering Microcontroller.
TIM15 can be synchronized with TIM16 and TIM17. TIM15, TIM16, and TIM17 have a complementary output with dead-time generation and independent DMA request generation. Their counters can be frozen in debug mode.

These timers are mainly used for DAC trigger generation. They can also be used as a generic 16-bit time base. The independent watchdog is based on a 12-bit downcounter and 8-bit prescaler for the purpose of Unlock MC68HC705C8A MCU Flash Memory. It is clocked from an independent 40 kHz internal RC and as it operates independently from the main clock, it can operate in Stop and Standby modes.
It can be used as a watchdog to reset the device when a problem occurs, or as a free running timer for application timeout management. It is hardware or software configurable through the option bytes. The counter can be frozen in debug mode only after Break MC68HC908EY16 Microprocessor Protected Flash.
The window watchdog is based on a 7-bit downcounter that can be set as free running. It can be used as a watchdog to reset the device when a problem occurs. It is clocked from the main clock. It has an early warning interrupt capability and the counter can be frozen in debug mode to facilitate the progress of Motorola M68HC711KA4 Flash Memory Replication.

